End-to-End Secure Engineering & Cybersecurity Support
Our teams embed security into development, infrastructure, and operational workflows.
Secure Application Architecture
Build platforms designed with security-first principles.
- Secure system design and threat modeling
- Identity and access control frameworks
- Privacy-by-design architecture
Data Protection & Compliance Support
Align your systems with modern regulatory expectations.
- GDPR-aware workflows and governance
- Secure data storage and encryption support
- Compliance documentation readiness
Identity & Access Management (IAM)
Ensure only the right users have the right access.
- Role-based access controls
- Authentication and authorization systems
- Secure enterprise identity workflows
Security Testing & Vulnerability Remediation
Identify weaknesses before attackers do.
- Application security testing (SAST/DAST)
- Vulnerability scanning and patch support
- Secure code review and remediation execution
Continuous Security Monitoring & Support
Security is ongoing — not one-time.
- Monitoring and incident response support
- Security posture improvements over time
- Long-term secure engineering teams
Cloud & Infrastructure Security
Secure cloud environments and infrastructure layers.
- Cloud security posture management and configuration reviews
- Container and infrastructure vulnerability scanning
- Secure network architecture and access policies
What You Can Expect
Engineering Ownership — Not Resource Allocation
Architecture-First Thinking
Predictable Sprint Execution
Retention & Continuity Managed
Built for Security & Scale
Remote Delivery Model
Our Remote Delivery Model
Outcome-focused execution. You define requirements, we deliver results.

Our Delivery Process
How We Structure and Scale Your Execution
Architecture review, stack alignment, risk assessment, and roadmap evaluation.
Sprint planning, backlog definition, technical standards, governance model setup.
Team onboarding, environment integration, workflow alignment.
Sprint execution, CI/CD releases, monitoring, performance tuning.
Own the Outcome. Skip the Complexity.
Intellibeans combines dedicated teams, structured processes, and performance accountability — so your business scales with confidence.
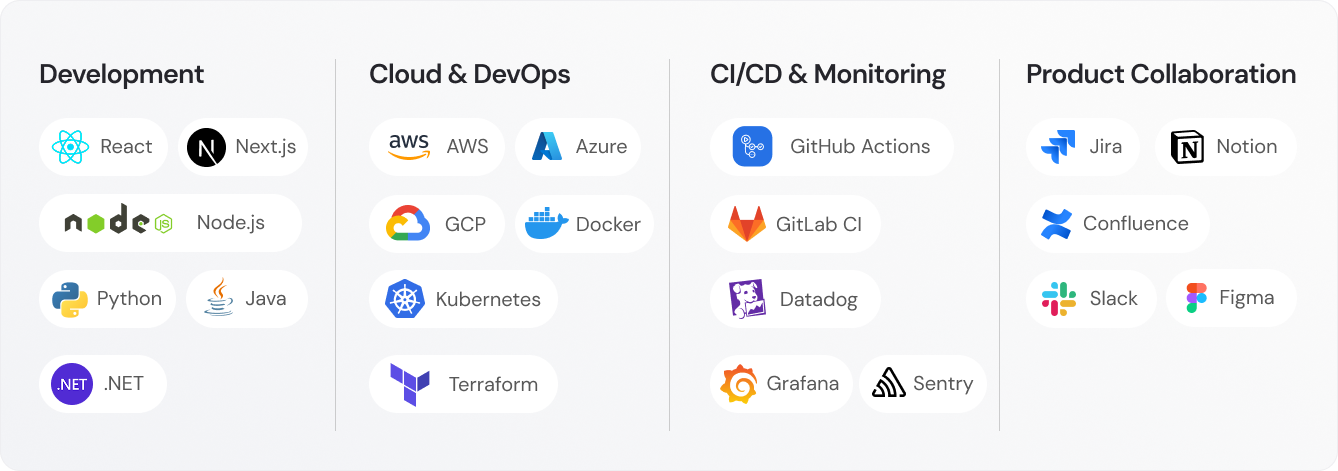
Tools We Use
Built With Proven, Modern Tools
Testimonial
Reviews From Our Clients
Real feedback from teams who trust us to deliver, scale, and support their products end to end.
Industries We Serve
Industry Expertise That Drives Results

Financial Services
Dedicated teams supporting financial institutions and fintech companies across software development, reporting operations, compliance workflows, reconciliation processes, automation, and secure data management.

Telecommunications
Execution teams supporting telecom providers with service workflows, compliance documentation, operational reporting systems, backend coordination, and customer support infrastructure.

Information Technology
Dedicated engineering and operations teams supporting IT companies with software development, cloud infrastructure, DevOps, cybersecurity support, analytics, and backend technical execution.

Retail and eCommerce
Scalable remote teams supporting ecommerce brands with platform development, order workflows, customer operations, marketing execution, automation systems, and performance analytics.

Healthcare
Compliance-aware execution teams supporting healthcare providers with administrative workflows, documentation management, reporting systems, insurance coordination, and secure backend operations.

Insurance
Execution teams supporting insurance providers with claims workflows, policy processing, compliance documentation, reporting systems, automation, and high-volume backend operations.
Technologies We Leverage
We support modern security-first delivery models including:


